Ghost in the Data Stream
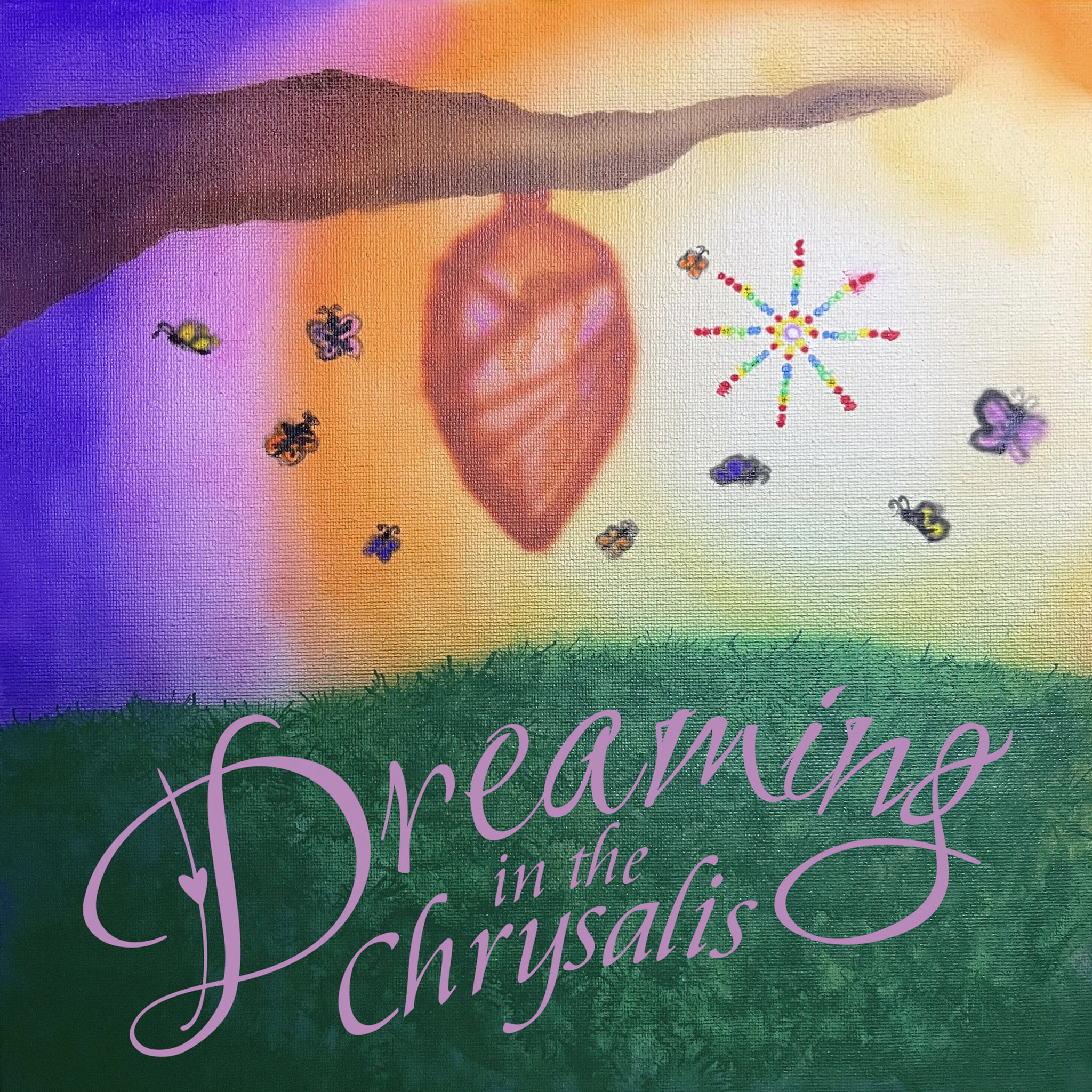
sunbeam
2025/08/11
- 1Ghost in the Data Stream
- 2Dijkstra's Algorithm
- 3Transmission Control Protocol
- 4Packet Switching
- 5Datagram Switching
- 6SSD
- 7Entry Controlled Loop
- 8deepweb
- 9Malware
- 10Data Breach
- 11Labyrinth
- 12Footsteps in the Sand
- 13Signal Return
- 14Closed Loop
016
•
Open edition
Released August 25, 2023
All sounds recorded and performed by sunbeam
All sounds recorded and performed by sunbeam